Posted on February 12, 2021
Content
Developers should also consider optimizing their web apps’ loading speeds, as the sluggish design is severely punished by terrible bounce rates. Single-page applications use dynamic routing so users won’t have to refresh or change web pages to load all of the available content for the application. Front-end and back-endframeworks and technologies can competently fulfill the requirements of your project.
In fact, it’s probably the case that you’re already very much in the know about several prominent web apps that are in frequent use across the web. Via Google Docs, users can interact directly with the web app by editing and making suggestions on documents. To do this, validate your prototype by presenting your web app to potential users. Python, Ruby, and PHP are some of the most popular back-end languages. Many tech companies use more than just one of these languages but still, many side-by-side comparisons exist to examine their utility.
For company-exclusive web apps, this means less time wasted and more time to be productive. To make the user experience more pleasant, program your search system to display related results in case of typographical errors. So if a user enters “ruining shoes” instead of “running shoes”, have your app pull up the best possible matches. One of the biggest mistakes that web app developers make is assuming that users will remember specific pieces of information. While some probably will, a good app doesn’t make this a requirement.
Imagine it’s such a relief as a customer to get viable solutions. The promptness in offering solutions can help to build valuable customer relationships. You would need to serve your web app through the HyperText Transfer Protocol Secure certificate.
Secrets to successful App development:
However, web applications place a certain focus on user interaction, just like a mobile app, and not like a traditional website at all. To design an Android or iOS app, a lot of groundwork is required. From conception to completion, precise planning is required. As the tech world continues to change, it’s important to keep up with trends and industry standards so your app can thrive in a competitive market.

Over time, your web app is going to accumulate a lot of information. If you’re managing an eCommerce shop, for example, you’ll eventually want to add more products as the business continues to grow. Web apps streamline business operations resulting in better productivity and sales.
Business Enquiry: business@prologictechnologies.in
UI UX design must be clear in mind so that you can communicate it to the app designer. You must have clarity on what is appealing to the audience. You must take into consideration the current color schemes, fonts, and logos to provide consistency. However, if you start afresh, you can adorn your creative hats and experiment with the app design. For example, if your app is aimed at kids, bright colors and easy-going language would serve the purpose.
PWAs definitely try to mitigate this side effect, but there’s no veritable evidence that they’ve successfully eliminated this disadvantage altogether. Distinguishing one from the other is admittedly nit-picky, but once you start recognizing the difference you’ll see why it matters. Yes, it’s true, in spite of being among the top factors of website design it’s still somehow underrated. It’s not necessary to fill every inch of your webpage with texts or images.
Today we are sharing the top 5 secrets of Android app development. Web applications are a cost effective solution rather than developing mobile applications that need constant updates and development. Web pages play a major role in our lives, with hundreds of websites surfacing on the internet the modern solution to different aspects of websites https://globalcloudteam.com/ has become a necessity. In the times of modern requirements and the process of making the technology a lot more well played than the past years, web application development came into the gameplay. In 2017, users downloaded 178.1 billion mobile apps to their devices worldwide, and this number is projected to grow to 258.2 billion by 2022.
accelerate your business.
There isn’t a one size fit all solution while choosing web development stacks. With so many technology options available for different components, it is a challenging task to choose the right one for your web project. Each tool has its own advantages and disadvantages and provides different results for different kinds of applications. Depending on your selection, you can make or break the functionality that you want to obtain in your application or software. Icreon has helped the company in designing a customized web platform with service-oriented architecture. The new web application has rules engine, report builder, workflow creator, making the entire visa application processes centralized and faster.
Therefore, you must have a solid idea of what you are going to create and why it is needed. Otherwise, your app is likely to go unnoticed by the audience in the app market. Hire a team of professional web developers and designers and see your vision come to life.
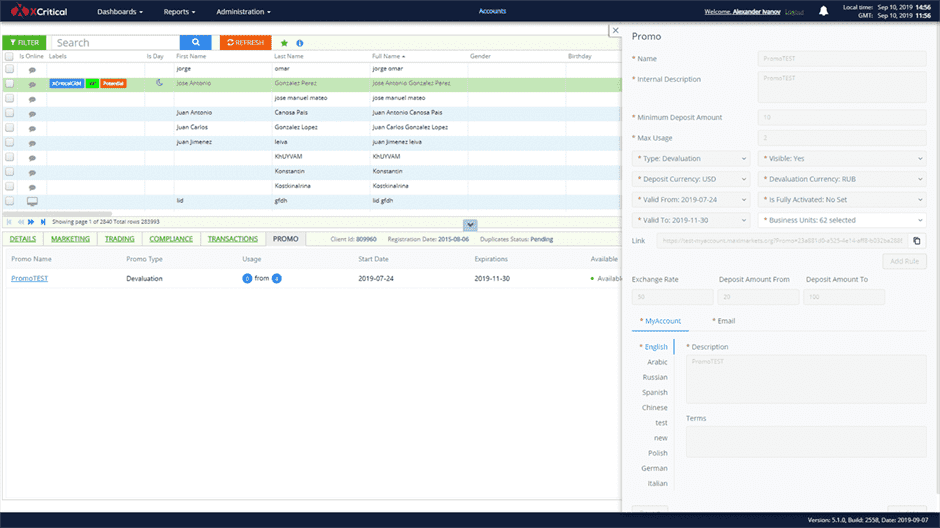
But if you don’t do it right, you could lose your SERP rankings and undo all of your hard work. Read this blog to find out how to redesign your website without losing SEO. ECommerce is rapidly changing together with modern technologies and online trends. Check out this blog to learn about its history, current trends, and future developments that may change the industry forever. Meanwhile, web apps that cater to customers need this feature to combat hacking attempts and malware injections. User rights management groups users according to their administrative privileges.
- “On our side, you would be in contact with the project manager and our own product manager on a regular basis, and with the development team during review calls.
- The app industry is opting for this idea to broadcasting their brands on the real platform.
- Although motion user interface design has been trending since 2018, SASS libraries technology has made accessibility easy for any device user.
- Given below are some popular frameworks that have large communities with many downloads.
- As for the options, you have three key options such as a native app, cross-platform native app, and hybrid app.
- While using Rust technology, it will take longer time to develop a web server since there are limited tools available.
This builds trust and loyalty among the brands and the users. Examine your target audience what they look forward to seeing in an app like yours. Evaluate their needs and wants to include features that meet their requirements. With a clear idea, purpose, and strategy, you can build an app with the potential to grow and succeed.
Why Frontend Developers Need to be Webpack Experts
It would help to constantly develop new features, consider the needs of the app users, and get a clear picture of what is working and what is not in the app. The Alpha test and Beta test are usually carried out for testing the app. Bringing resources into effective action can be tedious and time-consuming.

Building a custom enterprise web application can help you solve this problem. However, you need to incorporate unique features in your web app in order to see success. But in reality, most everyone in the software development industry believe web apps and hybrid apps have slower performance than native apps. In the end, web application development is quite a necessity today. It is far fetched technology and is sure to leverage the business in a significant amount.
Cybersecurity Ventures Report highlights that cybercrime is likely to cost the world $6 trillion per year by 2022. Healthcare, transport, marketing, and more are likely to be major IoT niches in 2022. Changes in the IoT environment will shape new trends in web design . You know that adage—“The only thing that’s constant is change.” As business owners, you need to keep looking at changing trends, changing patterns, and needs.
Services
The Internet of Things is a network of interconnected devices that require almost no actions from the users’ side to execute operations and perform useful results. Artificial Intelligence and Bots App-based chatbots interact efficiently with users. Typically, the bots use AI techniques such as natural language processing and pattern recognition to store and distinguish the context of the information provided.
Understanding How To Utilize Scrolling
Market research helps you gain insight into your target audience. This, as a result, will help you with the right set of features and requirements for your app. Prior research is very beneficial before you actually get into the development part.
In such a competitive market, if this service isn’t offered, many mobile app users will simply go elsewhere to a competitor that does offer it. That being said, when it comes to Android app development, heavily consider the application’s capabilities when it comes to cloud storage data solutions. However, businesses often face a hard time connecting with the target audience. Mobile apps are a medium that provides exposure through various platforms simultaneously. Businesses can use apps to send promotional offers via notification.
Native technology will always carry an advantage over non-native technologies. Since web apps aren’t native, they don’t have the same capacity to collaborate effectively with the hardware and operating system of your specific device. Once features and secrets of web app development again, most mobile app developers and web developers are not one and the same. This is a shame because that means if you want the best of both worlds, you’ll always need at least twice as many developers or at least twice as much talent.
For such projects, full stacks like MEAN or MERN can work the best. MEAN is a popular tech stack stands for MongoDB , Express.js , Angular (front-end framework), and Node.js . Whereas MERN is a tech stack containing MongoDB, Express.js, React/Redux, and Node.js technologies. Your website and app give you the much-needed drive that highlights the products and also, services you offer.